ABOUT
PRODUCTS
PARTNER WITH US
Get started today,
sign up for a free trial
Introspectus Software Assurance Management (SAM) gives IT leaders and procurement teams a single, authoritative view of every software licence across the organisation – from discovery to disposal, with the evidence to act.
Software asset management is not an IT housekeeping exercise. Done properly, it directly reduces operational expenditure, eliminates audit liability, and gives procurement teams the data they need to negotiate vendor contracts from a position of strength.
Most organisations are hit by the same three pressures: unexpected vendor audits that trigger massive unplanned costs, licence waste that compounds every renewal cycle, and a surge of unsanctioned SaaS tools that bypass policy entirely.
Together, they create financial, compliance, and security risks that traditional asset management can’t keep up with.
Introspectus SAM follows a logical flow – from discovery through to audit readiness – that mirrors how experienced SAM practitioners think.
Eliminate the blind spots and build boardroom confidence.
This allows organisations to achieve:
Lightweight agents scan every device and build a live software and hardware inventory within hours.
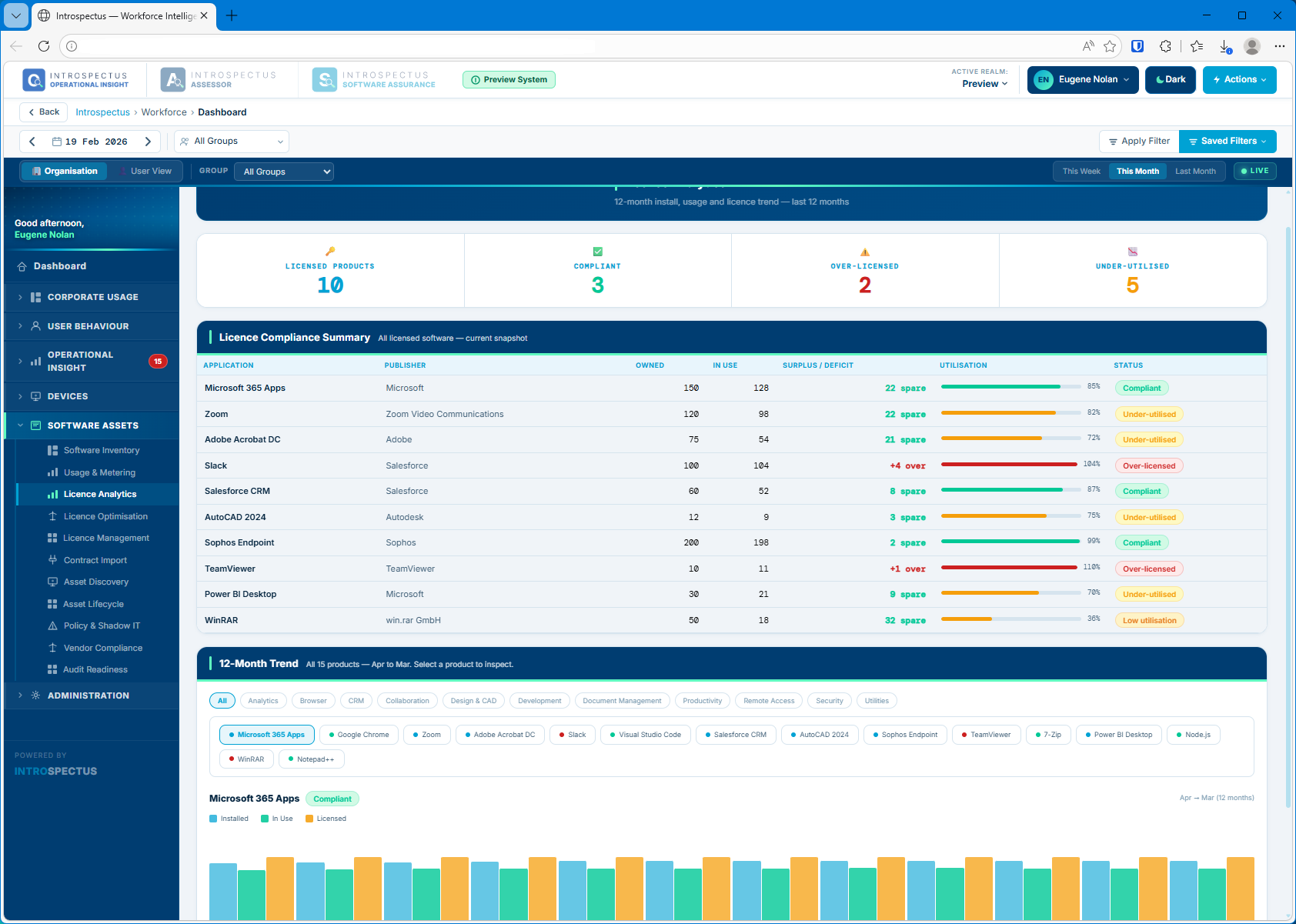
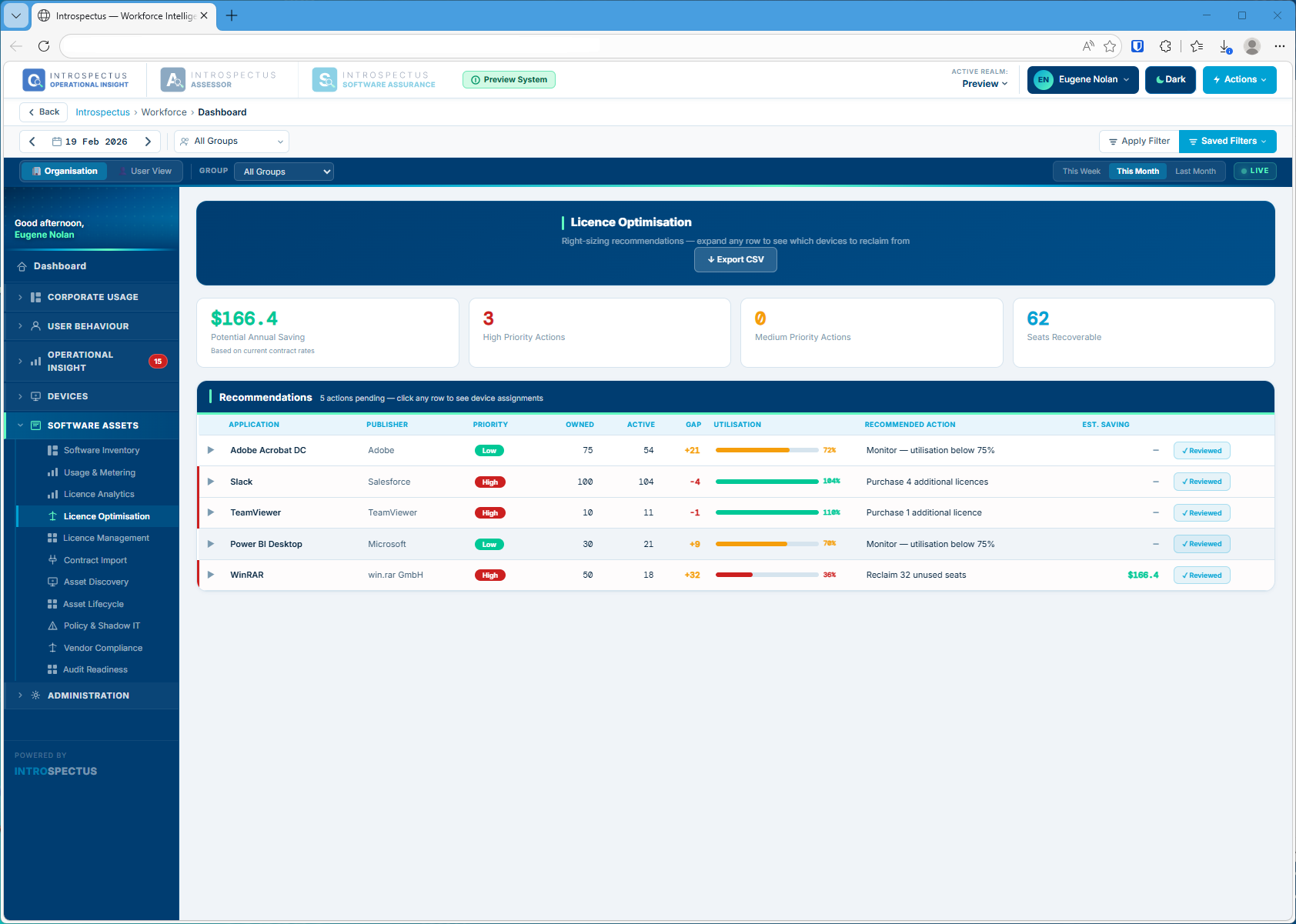
The platform compares usage to entitlements and highlights reclaim candidates with clear annual savings.
Audit Readiness generates an effective license position on demand with exportable evidence for audits.
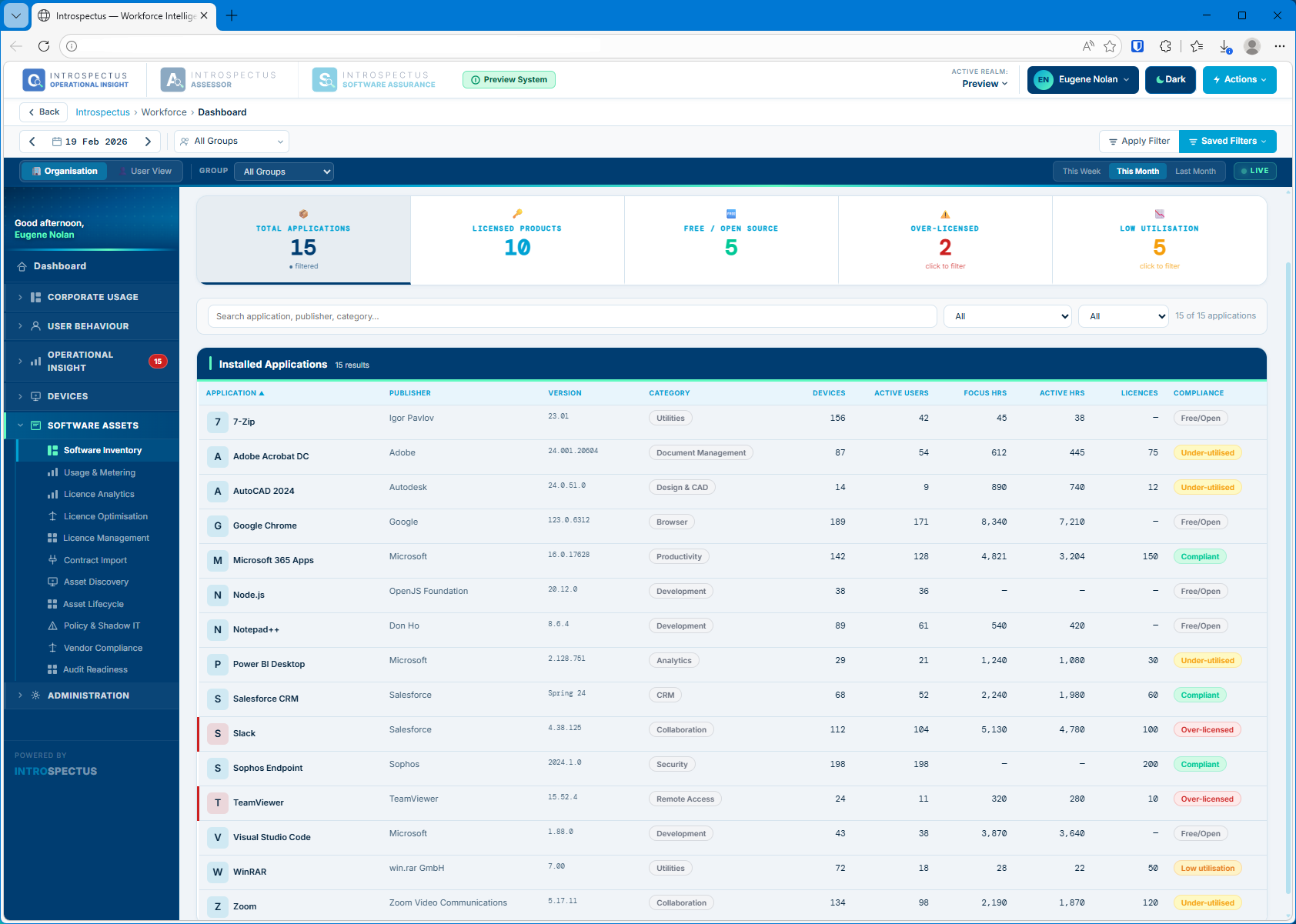
A real-time, agent-driven inventory of every application installed across your fleet – with the ability to drill from any title directly to the specific devices and users where it’s installed, how many hours they have used it this month, and whether their seat is covered by a current licence.
When TeamViewer runs on 24 devices against a 10‑seat licence, the system flags the breach, identifies unlicensed devices and highlights zero‑activity users.
The Users tab ranks every licence holder by monthly hours used, surfacing zero‑activity users as reclaim candidates with last‑active dates for manager conversations.
Export the full device list for any software title as a CSV sorted by usage with licence status, site and last‑active date included.
Software vendor audits – Microsoft true-ups, Adobe compliance checks, Oracle GLAS reviews – are increasingly common and increasingly costly. Introspectus gives you the position and the evidence before you need it.
| Effective Licence Position (ELP) | Vendor-Specific Compliance Rules |
|---|---|
| Generate a real-time ELP for any software title at any time, showing licences owned, deployed, active, and the variance – in a format auditors accept. Export to CSV for external review in one click. | Publisher licence metrics vary significantly. Microsoft counts named users; Oracle counts processor cores; TeamViewer counts concurrent sessions. Introspectus maintains a rule framework for each major publisher. |
| ✓ Exportable ELP on demand | ✓ Microsoft · Adobe · Salesforce · Zoom · Autodesk |
| SAM Audit Log | Evidence Export Package |
|---|---|
| Every change to licence counts, compliance status, contract records and vendor rules is captured in an immutable audit log – timestamped, attributed to a named user, and searchable. | The Audit Readiness module bundles your ELP, software inventory, contract register, usage evidence, device scan records, audit log and vendor compliance notes into a single downloadable package. |
| ✓ Immutable, timestamped record | ✓ Audit-ready in minutes |
| Policy and Shadow IT Governance | Asset Lifecycle Management |
|---|---|
| Classify every application as Approved, Monitored, Under Review or Blocked. Surface shadow IT – high-risk applications that are active but not sanctioned – with full usage context. | Track every software title from procurement through to retirement with a visual Kanban lifecycle board. Retirement checklists ensure licences are reclaimed, contracts archived and users notified. |
| ✓ Shadow IT detection built in | ✓ Procurement to Retired workflow |
Introspectus SAM is delivered as 11 integrated modules covering the full lifecycle from asset discovery through to audit defence. All modules are included; none are sold separately.
Fleet scan coverage dashboard with agent deployment status, version tracking and stale-agent detection.
Kanban lifecycle board from procurement to retirement, with renewal countdowns and retirement checklists.
Application and URL governance with shadow IT exposure detection and unsanctioned-domain alerting.
Publisher-specific licence metric frameworks for Microsoft, Adobe, Salesforce, Zoom, Autodesk and more.
Complete fleet-wide software discovery with device drill-down, compliance status and linked contract data.
Application focus hours, active users, session counts and peak-usage data linked to licence entitlements.
12-month trend charts showing installs, active usage and licence levels per software title.
Right-sizing recommendations with per-device reclaim guidance and estimated annual savings.
Structured contract register with renewal tracking, invoice management and vendor relationships.
AI-assisted extraction of contract data from uploaded documents — single or batch, ready for review in seconds.
SAM is a cross-functional discipline. Introspectus is designed to give each stakeholder the information they need in the context they work in.
Senior IT leaders need to know the organisation is not accumulating audit liability and that software spend is defensible to the CFO and board.
For practitioners responsible for the day-to-day SAM function, Introspectus replaces manual reconciliation with automated discovery and structured workflows.
Finance stakeholders need software costs to be predictable, justifiable and optimised. Introspectus provides usage evidence, savings projections and audit defence.
Ready to take control of your software estate?
Talk to our team about how Introspectus SAM fits your organisation’s size, complexity and existing tooling. Most customers are live within days – not months.
See the full SAM platform in action with your own use cases. Sessions run 45–60 minutes with a senior product specialist.
A two-page summary of Introspectus SAM capabilities, integration options and deployment models for internal circulation.
A scoped, time-limited deployment against your own fleet – giving your team direct experience before a commercial decision.
Each agent compares the current patch list against what is actually installed on its device. Any gap between what has been released and what is deployed is immediately surfaced. Critically, Introspectus pays particular attention to the timing of patch deployment not just whether a patch is present, but when it was applied.
This temporal dimension is central to Essential Eight compliance, where the difference between a patch applied on day two versus day thirty can mean the difference between maturity levels, and between an environment that was protected and one that was exposed.
This combination of daily patch intelligence, severity-based filtering, agent-level validation, and deployment timing analysis gives organisations a real-time, evidence-based view of their operating system patch posture mapped directly to the ISM controls applicable to the Essential Eight patch operating systems strategy.
The visibility gap here is particularly consequential. A patch may be approved and scheduled, yet never successfully applied due to a failed deployment, a device that was offline during the maintenance window, a reboot that was deferred, or a system that exists outside managed channels entirely.
Organisations that rely solely on deployment tooling to confirm patch status are measuring intent, not reality. The ACSC is explicit on this point: organisations need to confirm patches have been applied successfully, not merely that they were dispatched.
Within the Essential Eight framework, patching operating systems is a core and non-negotiable control. The ACSC sets clear expectations: patches for internet-facing infrastructure must be applied within 48 hours when identified as critical or where working exploits exist, and within two weeks for standard releases.
Patches for workstations, servers, and network devices must be applied within one month, with tighter timeframes applying in high-threat environments. Critically, the ACSC also mandates that vulnerability scanning occurs at least daily for internet-facing systems and at least fortnightly for workstations and non-internet-facing infrastructure not to replace patching, but to confirm it has actually occurred.
From this inventory, Introspectus performs targeted web intelligence gathering. For each application identified, the platform locates the top five authoritative sources of patch and release information vendor security advisories, release notes, and vulnerability databases and retrieves that content into a central repository.
Aletheia, Introspectus’s AI analysis agent, then reads and analyses this content to extract the intelligence that matters for application patching: the latest available version, whether a release addresses a security vulnerability, the severity of that vulnerability, and all information relevant to the Essential Eight application patching requirements. This structured intelligence is mapped directly to the applicable ISM controls, producing defensible, audit-ready evidence of an organisation’s application patch compliance posture.
A critical and frequently overlooked problem is the visibility gap. Organisations may believe their applications are current when, in reality, patches have silently failed, devices have missed deployment windows, or software has been installed outside of managed channels entirely.
Without continuous inspection at the endpoint level, these gaps go undetected until an audit or, worse, a breach.
Within the Essential Eight standard, patching applications is a dedicated and non-negotiable control. The ACSC specifies clear timeframes: critical vulnerabilities in internet-facing services must be addressed within 48 hours, commonly used applications such as office productivity suites, web browsers, email clients and PDF software must be patched within two weeks of release, and all other applications within one month.
For organisations in high-threat environments, the bar is higher still. Meeting these requirements consistently across hundreds of distinct applications deployed across thousands of endpoints is not achievable through manual effort alone.