- Home
- Essential Eight Cybersecurity Strategies
- Configure Microsoft Office Macro Settings
Configure Microsoft Office Macro Settings
What are Microsoft Office Macros and how do they work?
Macro malware hides in Microsoft Office files. Any Microsoft document can contain embedded code (Macros) written in Microsoft’s Visual Basic for Applications (VBA) programming language. These Macros can contain a series of commands that can be recorded and replayed at a later time. Macros are a legitimate functionality in Microsoft documents and are very useful. However, Macros can also be used to perform malicious activities.
Bad actors use Microsoft files with embedded Macros as part of phishing emails targeting users within an organisation. When a user opens the file, the Macro executes, performing malicious activity. This technique is one of the most prolific ways of compromising an organisation’s network and has a very high success rate.
It is difficult for anti-virus software to determine which Macros are malicious; as the software may be behaving as designed.

Why are Microsoft Office Macros important?
The purpose of Application Control is to create multiple layers of security to make it increasingly difficult for bad actors to run malicious code in a target organisation. If one layer is breached, multiple security measures remain to protect the organisation’s computer systems.
Traditional Antivirus software cannot block applications when they encounter new, unknown malware, especially in cases where an organisation is being targeted by a sophisticated bad actor.
Application Control protects against unknown malware by only allowing known and trusted applications and scripts to run within the organisation.
Introspectus Key Features
What's the solution?
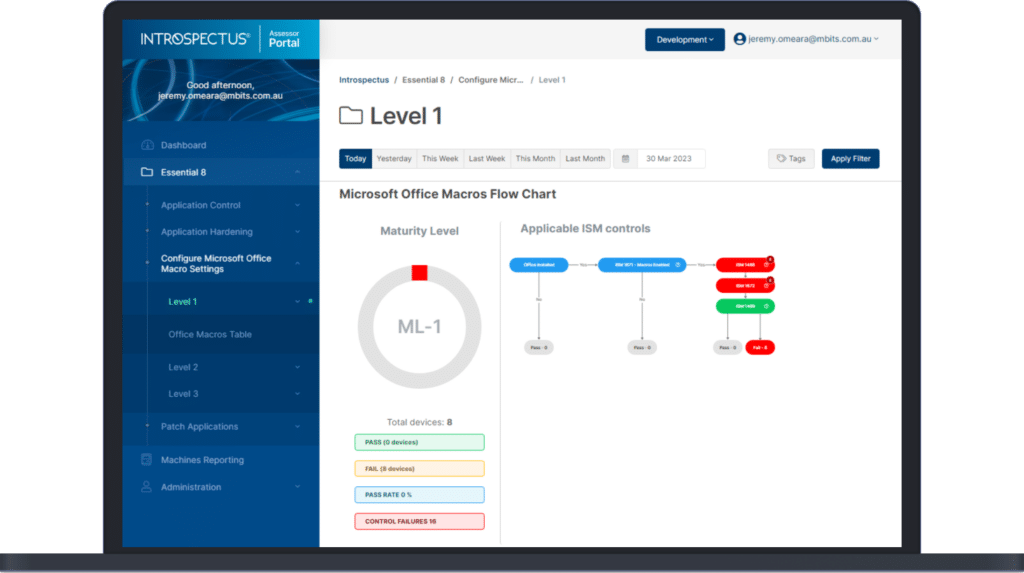
Introspectus analyses the Microsoft Office settings which have been applied in an organisation to determine whether Macro settings have been deployed in keeping with the recommended configurations outlined by ACSC.
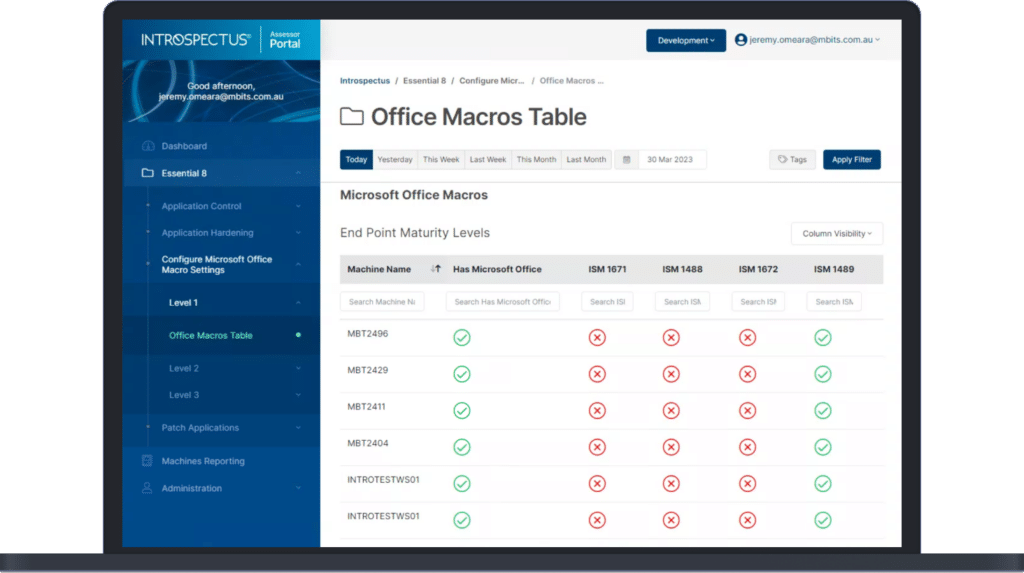
Introspectus software generates reports on Macro settings that confirm whether:
- Microsoft Office Macro settings are effective.
- Microsoft Office Macro settings have been deployed to all endpoints.
- Legacy versions of Microsoft Office are installed.
Automated Daily Tests
Introspectus performs a complete audit of Macros settings every day to provide organisations with confidence that their Macro settings are effective.
Device Audit Report
Introspectus confirms that the Microsoft Office software on devices is current.