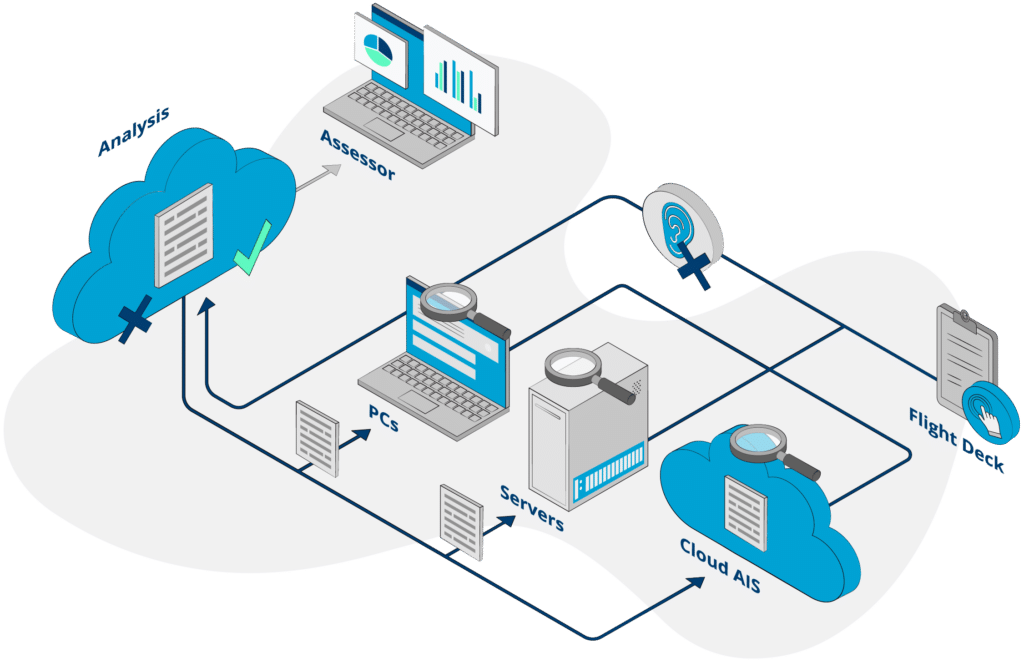
How It Works
Introspectus Assessor automates the testing of your organisation’s Essential Eight maturity so that you can mitigate cyber security risks and be confident in your security posture.
Introspectus Assessor
Technical Features
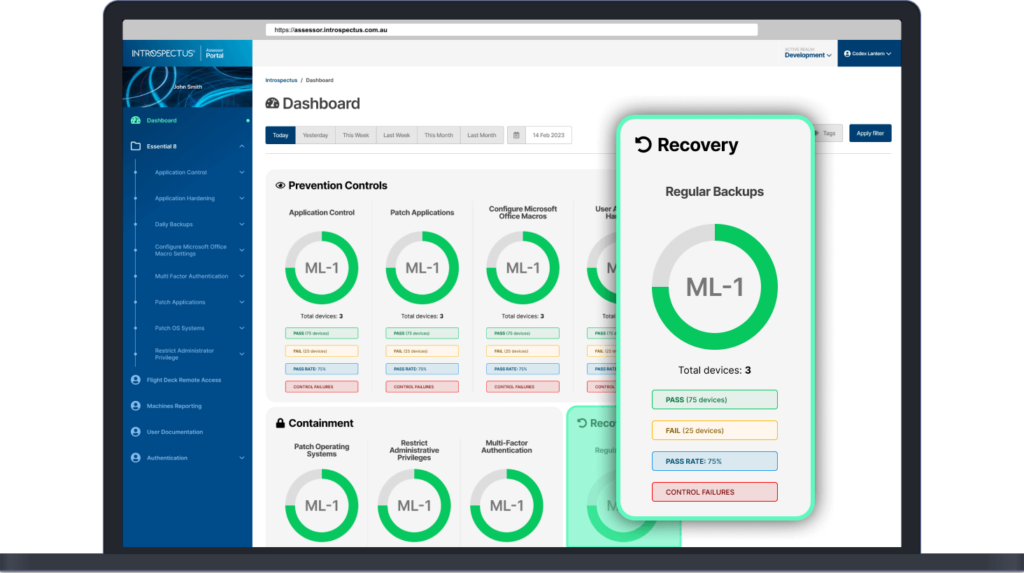
Technical Dashboards
Drill-down to individual device data.
Flight Deck
Confirm compliance. Scan a workstation or server in real-time, adjust and re-test.
Security
End-to-end encryption of all data in-transit and at-rest, two-factor authentication for secure access to Portal and Flight-Deck.
Performance
Minimal CPU overhead for Agent.
Customisable Testing
Assistance in design of rules to test your environment in addition to those supplied.
Remediation Advice
Details on how to implement ISM controls.
Introspectus Assessor
and the Essential Eight
The threat of cyber-attack is a persistent and growing concern for organisations of all sizes and in all industries. Each year, more organisations are finding that their risk mitigations have not been enough to keep cyber hackers out and then find themselves front page news.
One of the best approaches to mitigating cyber risk for your organisation is through the implementation of the Essential Eight Maturity Model.
The Essential Eight are the eight baseline mitigation strategies that are recommended to help protect your organization from various cyber threats. Implementing the Essential Eight security controls can help to mitigate up to 85% of cyber incidents.
These strategies are designed to counteract the most common and severe cyber threats, and have been shown to be effective in reducing the likelihood of a successful attack.
Implementing the Essential Eight, with in excess of 1,000 security controls to manage, and keeping your maturity level current, can be very daunting without dedicated resources to carry out audits on a regular basis, and perform any resultant remediation. Also, with so many controls, it can be almost impossible to be across all of their requirements and know where and how to set them.
Introspectus Assessor was created to...
Provide ongoing testing of
the controls
Automate the reporting of your organisation’s Essential Eight maturity
Give you details of your security posture to report to management; and
Provide information about controls that are not working, per device, with advice on how to fix them.
Share With Your Manager today
Download a high-level managerial overview of Introspectus Assessor to share with your Manager.
Download a Limited Free Trial
A no obligation free trial of Introspectus Assessor gives insight into the capabilities and control gained from real-time reporting and technical advice to overcome any security gaps and improve your security posture.
for Windows 64bit
